Chess Steganography Breakthrough 2026: High-Capacity PGN Encoding with Variations

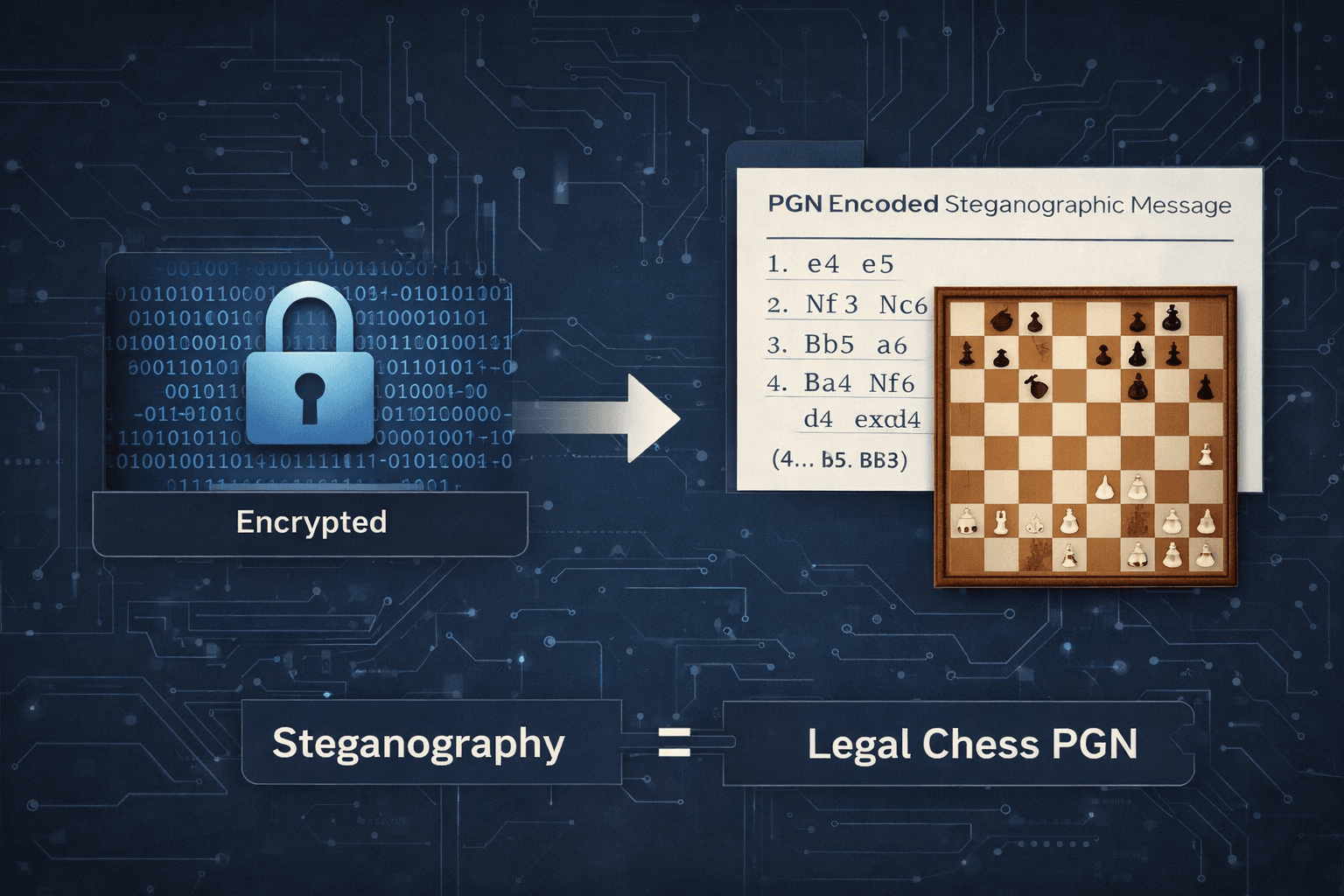
For over two decades, chess steganography has explored a simple idea: hide information inside legal chess games. Unlike image or audio steganography, chess offers something structurally different—messages disguised as normal PGN files shared daily on Lichess and Chess.com.
The problem was never possibility.
It was scalability.
Linear move-based systems rarely exceeded 50–200 bytes before games became suspiciously long. Even AI-assisted approaches for Chinese Chess (2025) averaged just ~51 bytes per game.
The 2026 variation-tree encoding method changes that constraint.
Instead of treating a chess game as a single linear sequence, it treats PGN as what it actually is: a tree structure.
Full technical research and benchmarks:
👉 https://www.rookduel.tech/research/Chess-Steganography-Breakthrough-2026
Why Previous Methods Were Limited
Earlier systems fell into two categories:
1. Multi-Channel Encoding (2004)
Used PGN headers, comments, formatting tricks, and legal moves.
Capacity reached several kilobytes—but at the cost of unnatural annotation patterns and weak encryption (XOR-based).
2. Linear Move Encoding (2009–2019)
Systems like chess-steg encoded bits by selecting from legal moves.
Typical characteristics:
~4 bits per ply
100–200 bytes practical ceiling
No encryption or integrity protection
Encoding ends when the game ends
Even AI filtering improved realism, not capacity. The structure remained linear.
The Shift: Variation-Tree Encoding
PGN natively supports variations:
1.e4 (1.d4 d5 2.c4) e5 2.Nf3 (2.Bc4 Nc6) Nc6
Serious analysis often contains deep nested branches. That structure is legitimate, standardized, and platform-supported.
Traditional Model
Game → Moves → End → Stop encoding
Variation-Tree Model
Game → Mainline + Nested Variations → Continue encoding across branches
Capacity now scales with branching depth, not just move count.
Core Architecture
Encoding Pipeline
Message
→ Brotli Compression
→ AES-256-GCM Encryption
→ Integer Conversion
→ Legal Move Selection
→ Standard PGN Output
Decoding
PGN
→ Move Extraction
→ Integer Reconstruction
→ Authenticated Decryption
→ Decompression
→ Original Message
Security properties:
AES-256 confidentiality
GCM authentication (tamper detection)
Optional PBKDF2 password protection
Encrypted timestamp + identifier metadata
Measured Capacity
Two representative tests:
Highly Repetitive Text (~86 KB)
Compressed to ~311 bytes
Encoded in 555 plies
~3.4 KB PGN output
~1 second encode time (consumer laptop)
Realistic Text (~88 KB)
Compressed to ~21.5 KB
Encoded across ~40,000 plies (mainline + 1,000+ variations)
~259 KB PGN
~5–6 minutes encode time (single-threaded laptop)
Effective rate: ~4.3 bits per ply.
Important: Larger payloads increase detectability. Capacity is technically high; operational use should remain conservative.
Practical Capacity Context
| Method | Practical Capacity |
| Linear chess encoding | 50–200 bytes |
| AI-filtered chess | ~50 bytes |
| Multi-method PGN (2004) | ~7 KB |
| Variation-tree encoding (2026) | 10–80+ KB (depending on risk tolerance) |
Improvement ranges from 10× to over 1000× depending on baseline comparison.
Security Model
This system provides:
✔ Cryptographic confidentiality (AES-256)
✔ Integrity verification (GCM tag)
✔ Standard PGN validity
✔ Legal move compliance
✔ Plausible deniability
It does not guarantee:
✘ Statistical indistinguishability
✘ Resistance to dedicated steganalysis at extreme payload sizes
Risk guidance:
<5 KB: low detection probability
5–20 KB: moderate analysis risk
20+ KB: increasingly suspicious
When This Makes Sense
Appropriate use cases:
Encrypted seed phrase backup
Secure key distribution
Covert configuration transfer
Research demonstration
Not appropriate:
Large binary files
High-surveillance adversarial environments
Payloads exceeding ~100 KB
Broader Insight
The breakthrough is structural:
Rule-constrained symbolic systems (like chess) become high-capacity steganographic channels when their native branching complexity is fully exploited.
The same principle could extend to:
Go
Shogi
Bridge bidding systems
Structured musical notation
Full Research & Benchmarks
This page is a condensed overview.
Complete methodology, formal discussion, benchmark data, and references are available here:
👉 https://www.rookduel.tech/research/Chess-Steganography-Breakthrough-2026
Author: Atharva Sen Barai
Published: February 2026
Live Demo: https://encode.rookduel.tech